Cybersecurity Operations Analyst and Incident Response Strategist :
Somewhere right now, an attacker is moving through a corporate network. They got in three weeks ago through a phishing email. They have mapped the environment, identified the domain controllers, found the backup servers, and positioned their payload. And the security team has no idea.
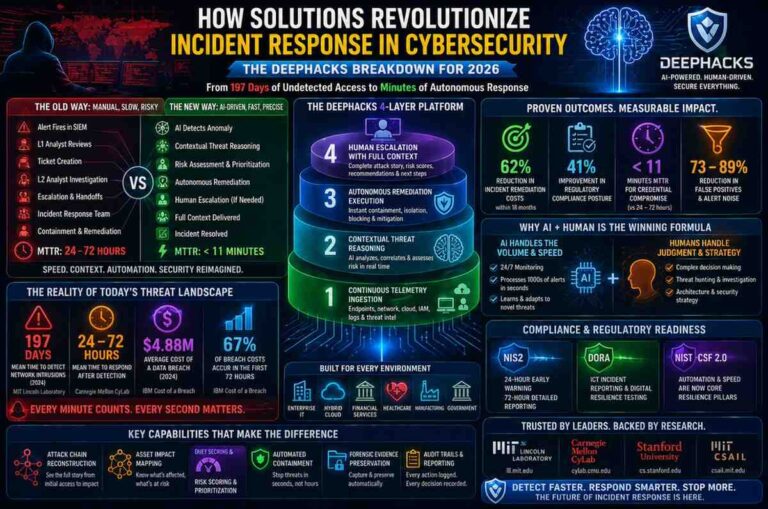
This is not a horror story. It is a documented pattern. The average time between a network intrusion and its detection was 197 days across mid-market organisations in 2024, according to research from MIT Lincoln Laboratory’s Cyber Security and Information Sciences division at ll.mit.edu. Almost seven months of undetected access. Enough time for an adversary to do anything they came to do, twice over.
The question every security leader is trying to answer in 2026 is simple: how do you close that gap? How do you move from detection measured in months to response measured in minutes?
That answer is what makes understanding how solutions revolutionize incident response in cybersecurity, specifically through platforms like DeepHacks, one of the most important operational conversations in the security industry right now.
What Incident Response Looks Like Today (And Why It Is Failing)
Before explaining what is changing, it helps to be honest about what is broken.
Traditional incident response follows a linear, human-driven process. An alert fires in the SIEM. An L1 analyst reviews it, determines whether it is genuine or a false positive, creates a ticket if it looks real, assigns it to an L2 analyst, who investigates and escalates if confirmed, who then engages the incident response team, who coordinate containment, remediation, and recovery. Every handoff adds time. Every queue adds time. Every shift change adds time.
The volume makes this model impossible to sustain at scale.
A 2024 study from Carnegie Mellon University’s CyLab Security and Privacy Institute at cylab.cmu.edu found that the average enterprise SOC analyst processed more than 4,400 security alerts per day. Nearly half of those alerts were false positives. The cognitive load of triaging that volume continuously is not a performance problem. It is a physiological one. Human attention degrades under sustained alert load. Critical signals get missed not because analysts are incompetent but because the system was never designed for this volume.
The results show up in the numbers:
- Mean time to detect (MTTD) for network intrusions averaged 197 days in 2024
- Mean time to respond (MTTR) for confirmed incidents averaged 24 to 72 hours even after detection
- The cost of a single data breach averaged 4.88 million dollars globally in 2024
- 67 percent of breach costs accumulate in the first 72 hours of uncontained compromise
Every hour between detection and containment is an hour the attacker continues operating inside the network. Every day between intrusion and detection is a day the attacker spends making themselves harder to remove.
This is the operational failure that next-generation solutions are built to eliminate. And it is the context that explains exactly why solutions revolutionize incident response in cybersecurity when they are built around agentic AI rather than human triage workflows.
[Image Placeholder: Side-by-side comparison timeline showing traditional manual SOC triage process with hours-to-days response versus agentic AI automated detection and remediation with seconds-to-minutes response]
What DeepHacks Is and Why It Represents a Different Category
DeepHacks is not a faster version of a traditional SIEM. It is not an upgraded SOAR with better playbooks. It is a fundamentally different architectural approach to incident response, one that applies agentic AI reasoning to security telemetry rather than rule-based pattern matching.
To understand why that distinction matters, consider how traditional security automation actually works.
SOAR (Security Orchestration, Automation and Response) platforms automate predefined playbooks. A security engineer sits down and writes: if this specific alert fires with these specific conditions, execute these specific response steps. The automation is only as capable as the scenarios its creators anticipated. Novel attack techniques, new threat actor behaviours, and unusual combinations of signals that do not match any existing playbook fall through the gaps and land back in a human analyst’s queue.
DeepHacks does not rely on predefined playbook rules. It applies large language model reasoning to security telemetry in real time. The system does not ask “does this match a known pattern?” It asks “what is actually happening here, and what is the most effective response given the current state of this environment?”
That is a categorical shift. Pattern matching is reactive and bounded by what was anticipated. Contextual reasoning is adaptive and capable of assessing novel scenarios without explicit programming.
The Four Operational Layers Where DeepHacks Changes Incident Response
[Image Placeholder: Layered architecture diagram showing four interconnected operational components of the DeepHacks platform from telemetry ingestion at the base to human escalation interface at the top]
Layer 1: Continuous Multi-Source Telemetry Ingestion
The platform ingests security telemetry from across the entire environment simultaneously: endpoint detection and response data, network traffic logs, cloud configuration states, identity and access management events, application logs, and external threat intelligence feeds. Normalisation happens in real time across all sources without manual correlation.
This matters because sophisticated attacks rarely generate obvious signals in any single data source. A credential stuffing attempt looks like authentication noise. Lateral movement looks like normal service account activity. Privilege escalation can resemble legitimate administrative action. The signal that confirms a genuine attack is usually the combination of weak indicators across multiple sources, assembled quickly enough to matter.
Human analysts correlating across five or six data sources simultaneously, under alert volume pressure, make mistakes. The DeepHacks ingestion layer does not.
Layer 2: Contextual Threat Reasoning
This is where the architectural difference between DeepHacks and traditional automation becomes most visible.
For each anomaly or alert cluster, the system builds a probabilistic threat assessment by applying contextual reasoning rather than rule matching. It evaluates: Is this alert pattern consistent with known attack chains? What is the likely intent based on the sequence and timing of events? What is the probable blast radius if this is a genuine compromise? Which assets are exposed downstream from the affected endpoint? What is the confidence level for this assessment given available evidence?
A login at 3am from an unusual geographic location means something completely different for a travelling executive who authenticated from five countries last quarter versus a service account that has never authenticated outside business hours and has no business reason to do so. Rule-based systems treat both identically. Contextual reasoning treats them correctly.
The system continuously updates its assessment as new telemetry arrives, adjusting confidence scores and threat classifications in real time as the picture becomes clearer or as the situation evolves.
Layer 3: Autonomous Remediation Execution
For confirmed or high-confidence threats, DeepHacks executes pre-authorised remediation actions immediately and autonomously. No ticket. No queue. No shift change delay.
Automated remediation actions available within the platform include:
- Endpoint isolation from the network while preserving forensic state
- Immediate credential revocation for compromised accounts
- Network micro-segmentation to block lateral movement paths
- Blocking of identified command-and-control communication channels
- Suspension of compromised service accounts with automated notification to owners
- Preservation of forensic evidence for post-incident analysis
These actions execute in under 60 seconds from confirmed detection. The difference between 60 seconds and 6 hours of containment time, at the point of an active ransomware deployment, is the difference between a contained incident and an organisation-wide encryption event.
Layer 4: Human Escalation with Full Context Delivery
For complex, ambiguous, or high-business-impact decisions, DeepHacks escalates to a human analyst. But it does not hand over a raw alert and a timestamp. It delivers a complete, structured context package assembled from everything the system has observed and reasoned about.
The escalation package includes: a reconstructed attack chain showing the sequence of events from initial access to current position, an affected asset map showing every endpoint and account involved, recommended response options with risk ratings for each, confidence scores for the threat assessment, and suggested investigation priorities for the human analyst to pursue.
An analyst receiving this package can make a high-quality decision in minutes rather than spending hours assembling the context manually. The human brings judgment, organisational knowledge, and strategic thinking. The platform provides the assembled evidence base that makes that judgment fast and accurate.
The Measured Outcomes: What Actually Changes
[Image Placeholder: Before and after metrics comparison chart showing MTTD, MTTR, false positive rate, and breach cost with and without agentic AI incident response]
The operational improvements from agentic AI incident response platforms are documented, not theoretical.
Carnegie Mellon’s CyLab research found that organisations deploying agentic AI in security operations achieved:
- 62 percent reduction in incident remediation costs within 18 months of deployment
- 41 percent improvement in regulatory compliance posture
- MTTR for credential compromise events compressed from 24 to 72 hours to under 11 minutes
- False positive noise reduction of 73 to 89 percent through contextual reasoning versus signature matching
Stanford University’s Department of Computer Science at cs.stanford.edu has published research on machine learning applications in network security showing that contextual anomaly detection systems operating on multi-source telemetry identify genuine threats with significantly higher precision than single-source signature-based detection, particularly for novel attack techniques not represented in historical training data.
The implication for security operations is direct. When analysts are freed from triaging thousands of false positives daily, they redirect that capacity toward higher-value activities: threat hunting, security architecture improvement, red team exercises, and strategic hardening of the environment. The AI handles the volume. The humans handle the complexity.
Why the Human Element Becomes More Important, Not Less
A common concern when organisations evaluate agentic AI security platforms is the question of whether automation reduces reliance on skilled security professionals. The operational reality runs in precisely the opposite direction.
MIT’s Computer Science and Artificial Intelligence Laboratory at csail.mit.edu, whose research on human-AI collaboration in high-stakes decision environments is extensively cited in security operations literature, has documented consistently that AI augmentation in complex decision environments elevates rather than diminishes the value of human expertise. The AI handles tasks where speed and scale create advantages. Humans handle tasks where judgment, context, and novel reasoning create advantages.
In a security operations context, this means:
- L1 triage becomes largely automated, freeing analysts for L2 and L3 work
- Threat hunting becomes possible because analysts have time for proactive investigation rather than reactive triage
- Incident response quality improves because humans engage with pre-assembled context rather than raw data
- Strategic security improvement accelerates because senior analysts spend time on architecture rather than alert queues
The organisations that extract the most value from platforms like DeepHacks are not the ones that use AI to reduce their security team headcount. They are the ones that use AI to dramatically increase what their existing team can achieve.
Implementation Considerations for Security Leaders Evaluating DeepHacks
For CISOs and security architects evaluating whether an agentic AI incident response platform belongs in their environment, the following considerations are worth working through before beginning a proof of concept.
Telemetry coverage before deployment. Agentic AI reasoning is only as good as the telemetry it receives. Before deploying a platform like DeepHacks, audit your current data source coverage. Gaps in endpoint visibility, cloud configuration monitoring, or identity log collection will create blind spots that the AI cannot compensate for regardless of reasoning quality.
Pre-authorisation scope definition. The autonomous remediation capability requires clear pre-authorisation boundaries. Which actions can the system execute without human approval? Endpoint isolation, credential revocation, and network segmentation all have different business impact profiles. Define these boundaries before deployment, not after the first automated action triggers an operational escalation.
Integration with existing tooling. Evaluate how the platform integrates with your current SIEM, EDR, ITSM, and identity management infrastructure. The value of contextual reasoning depends on the platform having access to data across your existing tool stack. Integration depth directly determines reasoning quality.
Escalation workflow design. The human escalation interface is not just a notification mechanism. It is a decision support system. Design escalation workflows that deliver the right information to the right analyst tier with the right urgency signal. Poorly designed escalation flows reduce the value of even excellent automated triage.
Baseline measurement before deployment. Establish documented MTTD and MTTR baselines for your current environment before beginning any deployment. Without a before measurement, you cannot demonstrate an after improvement. This matters for security program justification as much as it matters for operational feedback.
The Regulatory Dimension: Why Agentic AI Incident Response Supports Compliance
The regulatory environment for cybersecurity incident response has become significantly more demanding in 2025 and 2026.
NIS2 (Network and Information Security Directive 2), effective across EU member states since October 2024, requires in-scope organisations to report significant incidents to competent national authorities within 24 hours of detection as an early warning, with a full detailed report within 72 hours. For organisations operating on manual detection processes with MTTD measured in weeks or months, these timelines are impossible to meet.
DORA (Digital Operational Resilience Act), effective January 2025 for EU financial entities, imposes similar incident reporting timelines with additional requirements for documented ICT risk management frameworks and annual digital operational resilience testing.
NIST’s Cybersecurity Framework 2.0, published in 2024 and available at nist.gov/cyberframework, now explicitly addresses the role of automation in incident response as a component of organisational resilience. The framework’s Respond function specifically calls for detection and response capabilities that operate at a speed proportionate to the threat environment, a standard that manual triage processes struggle to meet under the current threat volume.
Agentic AI incident response platforms support regulatory compliance not just by improving response speed but by generating auditable records of every detection, reasoning step, automated action, and escalation decision. For organisations facing NIS2 or DORA audits, that audit trail is a compliance asset with direct value independent of the operational improvements.
Frequently Asked Questions
What exactly does DeepHacks do that traditional SOAR platforms cannot?
DeepHacks applies contextual reasoning to security telemetry rather than matching alerts against predefined playbook rules. Traditional SOAR platforms can only automate scenarios that were explicitly anticipated by the engineers who wrote the playbooks. DeepHacks can reason about novel attack patterns, unusual combinations of signals, and threat scenarios that have no existing playbook by building a probabilistic threat assessment from available evidence. This makes it effective against both known attack patterns and novel techniques that bypass signature-based detection.
How do solutions revolutionize incident response in cybersecurity compared to older automation tools?
Older automation tools in cybersecurity operated on fixed rules: if a specific condition matches, execute a specific response. This approach is fast but brittle. Modern solutions like DeepHacks use agentic AI to reason contextually, meaning they assess what is actually happening in the environment and select responses based on the specific situation rather than a matching rule. The result is faster response, fewer false positives, and the ability to handle threats that do not match any predefined pattern. This is the fundamental shift that makes these solutions a genuine revolution rather than an incremental improvement.
What types of organisations benefit most from agentic AI incident response?
Organisations with distributed or complex network environments, high daily alert volumes, compliance requirements for rapid incident reporting (NIS2, DORA, HIPAA, PCI DSS), limited SOC analyst headcount relative to monitoring scope, or hybrid cloud infrastructure with multiple data sources all see disproportionate benefit from agentic AI incident response. The value scales with the complexity of the environment and the gap between current analyst capacity and the monitoring scope required.
Is agentic AI incident response suitable for smaller security teams?
Yes, and in some ways smaller teams benefit more than larger ones because the analyst capacity constraint is more acute. A five-person SOC using agentic AI for L1 triage can direct all five analysts toward L2 and L3 work, threat hunting, and strategic improvement. Without automation, those same five analysts spend the majority of their time on alert triage that produces limited security value. The platform does not replace the team. It multiplies what the team can accomplish.
What are the risks of autonomous remediation actions in production environments?
The primary risks are operational disruption from automated actions that are correct from a security standpoint but disruptive from a business standpoint, such as isolating an endpoint that a critical business process depends on. These risks are managed through pre-authorisation scope definition: the security team specifies which actions the system can take autonomously and which require human approval before execution. Starting with a conservative pre-authorisation scope and expanding it as confidence in the system grows is the standard deployment practice for mature agentic AI implementations.
How does DeepHacks handle compliance reporting requirements under NIS2 and DORA?
The platform generates auditable records of every detection event, reasoning chain, automated action taken, and escalation decision made throughout the incident lifecycle. These records provide the documented evidence base required for NIS2 early warning reports (due within 24 hours of detection) and detailed incident reports (due within 72 hours). For DORA-regulated financial entities, the same audit trail supports ICT incident reporting obligations and provides evidence of the documented ICT risk management framework required by the regulation.
Final Perspective: The Window for Action Is Shorter Than It Looks
The gap between where most organisations are today and where they need to be in terms of incident response speed and capability is real, measurable, and closing from the wrong direction.
Threat actors are deploying faster. Ransomware groups have compressed their dwell-to-encryption timelines from weeks to hours. Regulators are demanding faster reporting. The cost of a contained incident versus an uncontained one continues to grow.
The solutions that revolutionize incident response in cybersecurity, built around agentic AI platforms like DeepHacks, exist specifically to close that gap. They are not experimental technology. They are production-ready platforms with documented outcomes, active enterprise deployments, and a growing body of independent research validating their performance advantages.
The organisations that deploy now are building operational advantages that compound over time: faster response, lower breach cost, better compliance posture, and a security team that spends its time on the work that only humans can do.
The organisations that wait are extending their detection gaps one quarter at a time.