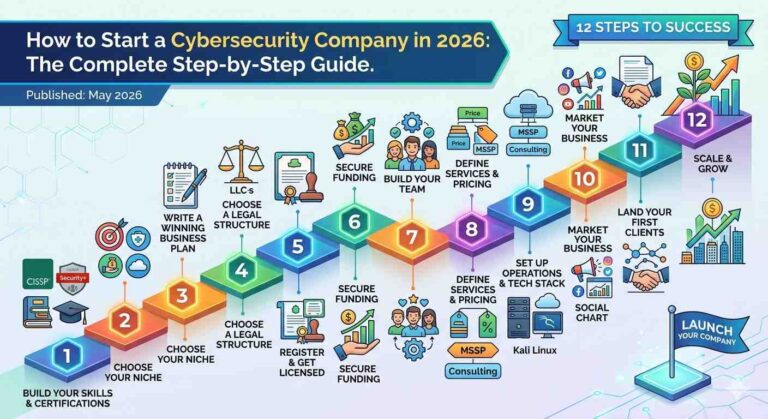
Table of Contents
- Why Start a Cybersecurity Company in 2026?
- What Does a Cybersecurity Company Actually Do?
- Step 1: Build Your Skills and Get Certified
- Step 2: Choose Your Niche
- Step 3: Write a Winning Business Plan
- Step 4: Choose a Legal Structure
- Step 5: Register Your Business and Get Licensed
- Step 6: Secure Funding
- Step 7: Build Your Team
- Step 8: Define Your Services and Pricing
- Step 9: Set Up Operations and Tech Stack
- Step 10: Market Your Cybersecurity Business
- Step 11: Land Your First Clients
- Step 12: Scale and Grow
- Common Mistakes to Avoid
- Frequently Asked Questions
- Final Thoughts
Why Start a Cybersecurity Company ?
There has never been a better time to launch a cybersecurity company. Cyber threats are escalating at an unprecedented rate, digital transformation is accelerating across every industry, and demand for skilled security professionals is outpacing supply by millions of positions.
The numbers speak for themselves. The global cybersecurity market was valued at over $271 billion in 2025 and is projected to grow to $663 billion by 2033, expanding at a compound annual growth rate (CAGR) of nearly 12%. According to Cybersecurity Ventures, global spending on cybersecurity products and services is expected to exceed $520 billion annually by 2026 — and could reach $1 trillion per year by 2031.
Cybercrime is a key driver of this explosive demand. The same research firm estimates that cybercrime will cost the world $10.5 trillion in 2025, up from $6 trillion in 2021. Every data breach, ransomware attack, or phishing campaign pushes businesses — large and small — to invest more in protection.
Perhaps most importantly for aspiring entrepreneurs: small and medium-sized businesses (SMBs) are desperately underserved. Large enterprises have the budget to build internal security teams, but the millions of SMBs worldwide cannot afford full-time cybersecurity staff. This creates a massive, recurring, and largely untapped market for boutique cybersecurity firms, managed security service providers (MSSPs), and consulting businesses.
Experienced cybersecurity consultants command rates of $150 per hour or more. If you have the skills, the market is ready for you.
What Does a Cybersecurity Company Actually Do?
A cybersecurity company specializes in protecting individuals, organizations, and digital systems from cyber threats, attacks, unauthorized access, and data breaches. Depending on your focus, your company might offer:
- Penetration testing (ethical hacking) — simulating real-world attacks to find vulnerabilities before criminals do
- Managed Security Services (MSSP) — ongoing monitoring and management of a client’s security infrastructure
- Incident response — helping organizations recover from cyberattacks and data breaches
- Security audits and compliance — ensuring clients meet GDPR, HIPAA, PCI-DSS, SOC 2, and other regulatory frameworks
- Vulnerability assessments — systematic scanning and analysis of systems and networks
- Security awareness training — educating employees to recognize phishing, social engineering, and other threats
- Cloud security consulting — securing cloud-native environments on AWS, Azure, and Google Cloud
- Virtual CISO (vCISO) services — providing fractional chief information security officer expertise to companies that cannot afford a full-time executive
Understanding which of these services aligns with your expertise is the critical first step before you do anything else.
Step 1: Build Your Skills and Get Certified
Your credibility is your currency in the cybersecurity industry. Before you can sell security services, you need to demonstrate deep, verifiable expertise. Clients are trusting you with their most sensitive data and critical systems — they will demand proof of competence.
Essential Cybersecurity Certifications
Entry-Level / Foundational:
- CompTIA Security+ — The industry’s most recognized entry-level certification, held by over 700,000 IT professionals. It is DoD-approved under the 8570/8140 standards, making it essential for government contracts. This is often the first certification aspiring security professionals should earn. Learn more at CompTIA’s official site.
- Google Cybersecurity Certificate — An accessible and affordable starting point available through Coursera, ideal for career changers building foundational knowledge.
Intermediate:
- Certified Ethical Hacker (CEH) — Offered by EC-Council, the CEH teaches professionals to think like a hacker. It is ANSI-accredited, DoD-approved under 8140 standards, and highly regarded for offensive security and penetration testing roles. CEH holders earn an average salary of around $134,000 per year.
- CompTIA CySA+ — Focuses on behavioral analytics, threat intelligence, and SOC-level analyst skills. Excellent for those building detection and response capabilities.
- GIAC Security Essentials (GSEC) — Provided by Global Information Assurance Certification, GSEC validates broad information security knowledge and is widely respected across industries.
Advanced / Leadership:
- Certified Information Systems Security Professional (CISSP) — Widely regarded as the gold standard of cybersecurity certifications, the CISSP is administered by ISC2 and covers eight domains of security knowledge, from risk management to software development security. It requires at least five years of paid experience in two or more domains. CISSP holders earn an average of $151,860 per year in the United States. You can learn more at ISC2.org.
- Certified Information Security Manager (CISM) — Issued by ISACA, CISM validates security management and governance expertise. CISM-certified professionals earn an average of around $150,000 per year in North America and is essential for those targeting executive or managerial roles.
- OSCP (Offensive Security Certified Professional) — The most respected hands-on certification for penetration testers, requiring candidates to pass a 24-hour practical hacking examination. It is ideal for red team service offerings.
Degree Programs
While certifications demonstrate practical skills, a bachelor’s or master’s degree in computer science, information technology, or cybersecurity strengthens your credibility further. MIT, Carnegie Mellon, and Stanford all offer respected cybersecurity programs. For a comprehensive overview of academic pathways, the National Initiative for Cybersecurity Education (NICE) at NIST provides excellent frameworks and resources.
The Reality of Continuous Learning
The threat landscape evolves every day. Your certifications are not a destination — they are a starting point. Plan to invest in continuous education through industry conferences (like DEF CON, Black Hat, and RSA Conference), online platforms (Cybrary, SANS Institute, Offensive Security), and hands-on practice through platforms like HackTheBox and TryHackMe.
Step 2: Choose Your Niche {#step-2}
One of the most critical decisions you will make is choosing a specific niche rather than attempting to serve every possible client with every possible service. The cybersecurity industry is vast, and generalists rarely win in a competitive market.
Specialization matters because:
- It allows you to develop deeper expertise faster
- It makes your marketing more targeted and cost-effective
- It enables premium pricing based on specialized knowledge
- It builds a stronger reputation within a specific community
Popular Cybersecurity Niches
By Industry Vertical:
- Healthcare — The healthcare sector is expected to grow at the highest CAGR in the cybersecurity market (nearly 19%), driven by HIPAA compliance requirements, connected medical devices, and electronic health records. Healthcare organizations are frequent ransomware targets and are willing to pay for specialized compliance expertise.
- Financial Services (BFSI) — Banks, insurance companies, and financial institutions hold the largest share of the cybersecurity market and face stringent regulatory requirements around PCI-DSS, SOX, and GDPR. This vertical demands CISM and CISA certifications.
- Government and Defense — Government contracts are lucrative and stable, but require DoD-approved certifications and often security clearances. This niche can provide long-term revenue stability.
- Manufacturing and Critical Infrastructure — Industrial control systems (ICS) and operational technology (OT) security is a fast-growing niche, as attackers increasingly target production systems and supply chains.
- Retail and E-Commerce — PCI-DSS compliance and protection against payment fraud drive strong demand in this sector.
By Service Type:
- Penetration testing and red team services
- Cloud security (AWS, Azure, Google Cloud)
- Managed detection and response (MDR)
- vCISO and security advisory services
- Security awareness training and phishing simulation
- Incident response and digital forensics
By Business Size:
- Serving enterprise clients requires complex proposals, longer sales cycles, and robust reporting capabilities
- Serving SMBs offers higher volume, faster sales cycles, and a massive underserved market
- Mid-market companies offer a balance of deal size and sales speed
Conduct a SWOT analysis (Strengths, Weaknesses, Opportunities, Threats) on each niche you consider, evaluate your existing expertise and network, and analyze the competitive landscape in your target geography before committing.
Step 3: Write a Winning Business Plan
A thorough business plan is not optional — it is the foundation of everything that follows. It guides your decision-making, helps you identify blind spots, and is essential if you ever need external funding.
Your cybersecurity business plan should include:
Executive Summary — A concise overview of your company, value proposition, target market, and why your business will succeed. Write this last, even though it appears first.
Company Description — Your mission statement, vision, core values, legal structure, and founding team’s background.
Market Analysis — A deep dive into your target market size, growth trends, customer pain points, and competitive landscape. Who are your direct competitors? Where are the gaps they are not filling?
Services and Pricing — A clear description of every service you will offer, how it is delivered, and your pricing model (hourly, retainer, project-based, or subscription).
Marketing and Sales Strategy — How you will attract and convert clients. Which channels will you use? What is your sales process? What is your estimated client acquisition cost?
Operations Plan — How you will deliver services. What tools, platforms, and processes will you use? How will you maintain quality control?
Financial Projections — Revenue forecasts for the first three years, startup costs, monthly operating expenses, and break-even analysis. Include best-case, base-case, and worst-case scenarios.
Funding Requirements — If you need investment, clearly state how much you need and how you will use it.
The U.S. Small Business Administration (SBA) at sba.gov provides excellent free templates and guidance for writing business plans.
Step 4: Choose a Legal Structure
The legal structure of your cybersecurity business has significant implications for taxation, liability, and future fundraising. The four most common structures are:
Sole Proprietorship — Simple and cheap to set up, but you bear full personal liability for any legal claims. This is rarely advisable for a cybersecurity company, where a client data breach could result in significant lawsuits.
Partnership — Suitable if you are co-founding with one or more people. A formal partnership agreement is essential to define roles, profit-sharing, and exit provisions.
Limited Liability Company (LLC) — The most popular choice for early-stage cybersecurity companies. An LLC separates your personal assets from business liabilities, offers tax flexibility, and has minimal administrative overhead. Most founders start as an LLC.
Corporation (C-Corp or S-Corp) — Required if you plan to raise venture capital, offer stock options to employees, or eventually pursue an IPO. C-Corps offer the most flexibility for outside investment but come with more regulatory and tax complexity.
Our recommendation: Start as an LLC. If you raise institutional venture capital or plan significant equity-based hiring, convert to a C-Corp at that point. Consult with a business attorney and accountant before making this decision, as state-specific factors also apply.
Step 5: Register Your Business and Get Licensed
Once you have chosen a legal structure, take the following steps:
- Choose and register your business name — Search state and federal trademark databases to ensure your chosen name is available. Then register it with your state’s Secretary of State office.
- Obtain an EIN (Employer Identification Number) — Apply for free at IRS.gov. Your EIN is required for opening a business bank account and filing taxes.
- Get required business licenses and permits — Requirements vary by state and locality. Many jurisdictions require a general business license. Check with your state and local government agencies.
- Open a dedicated business bank account — Keep your personal and business finances completely separate from day one. Look for fee-free business checking accounts and consider a business credit card for expense tracking.
- Consider cybersecurity-specific compliance requirements — If you handle client data, you may need to comply with regulations like GDPR (for European clients), CCPA (California), or sector-specific rules like HIPAA. Build compliance into your operations from the start, not as an afterthought.
- Get business insurance — At a minimum, obtain general liability insurance. More importantly for a cybersecurity firm, get professional liability insurance (errors and omissions) and a cyber liability policy. If you have employees, workers’ compensation is also required in most states.
Step 6: Secure Funding
Your startup costs will depend on your business model. A solo cybersecurity consultant can launch for as little as $5,000–$15,000, covering primarily certifications, software tools, legal fees, and marketing. A fully staffed MSSP or product company will require significantly more capital.
Funding Options
Bootstrapping — Many successful cybersecurity firms are self-funded. The consulting model generates revenue quickly, and early client payments can fund growth. This gives you full control but limits your growth speed.
Small Business Loans — The SBA offers loan programs specifically for small businesses. The SBA 7(a) loan is the most common, offering up to $5 million for qualified borrowers. Visit sba.gov/funding-programs/loans for details.
Angel Investors — High-net-worth individuals who invest in early-stage companies in exchange for equity. Cybersecurity is a hot sector for angel investment. Look for angels with technology or security industry backgrounds who can also provide mentorship and introductions.
Venture Capital — VC funding is appropriate for cybersecurity product companies with significant market potential and scalability. Firms like Evolution Equity Partners, DataTribe, and Ten Eleven Ventures specialize in cybersecurity investments.
Government Grants and Contracts — The U.S. Small Business Innovation Research (SBIR) program provides non-dilutive funding for small businesses conducting R&D with commercial potential. Government cybersecurity contracts through agencies like CISA and DoD can also provide substantial early revenue.
Revenue-Based Financing — A growing alternative for service businesses, allowing you to borrow against future revenue without giving up equity.
Step 7: Build Your Team
When starting a cybersecurity firm, your people are your most valuable competitive advantage. The quality of your team determines the quality of your service delivery and, ultimately, your reputation in the market.
Key Roles to Consider
For a Consulting/Services Firm:
- Penetration testers and ethical hackers
- Security analysts (SOC Tier 1, 2, 3)
- Cloud security engineers
- Compliance specialists (HIPAA, PCI-DSS, GDPR)
- Incident response specialists
- Business development manager
For an MSSP:
- SOC analysts (24/7 coverage requires rotating shifts)
- Threat intelligence analysts
- Security engineers
- Account managers
Hiring Strategies
- Certifications matter — Prioritize candidates with CISSP, CEH, OSCP, CISM, and CompTIA Security+ certifications. According to CyberSeek, 89% of hiring managers will not interview uncertified candidates for security roles.
- Hire for culture and ethics — You are handling sensitive client data. Integrity is non-negotiable. Conduct thorough background checks.
- Start lean, then scale — Many successful founders start as solo operators, bring on one or two contractors for specific engagements, and hire full-time staff only when revenue supports it.
- Consider remote talent — The cybersecurity talent shortage is real. ISC2 estimates a global shortfall of 3.4 million cybersecurity professionals. Embrace remote hiring to access a larger talent pool.
- Invest in continuous training — The threat landscape changes constantly. Budget for ongoing professional development, certification renewals, and conference attendance.
For recruiting, platforms like LinkedIn, CyberSecJobs, and SANS job boards are excellent resources. Building relationships with university cybersecurity programs also creates a steady talent pipeline.
Step 8: Define Your Services and Pricing
Defining your services clearly and pricing them strategically is critical to your business’s sustainability and growth.
Common Cybersecurity Service Models
Hourly / Time-and-Materials — Best for ad hoc engagements, incident response, and one-time assessments. Experienced consultants typically charge $150–$300+ per hour depending on specialization and geography.
Project-Based Fixed Fee — Best for penetration testing engagements, security audits, and compliance assessments with well-defined scopes. Pricing varies widely: a small network pen test might run $5,000–$15,000, while a comprehensive enterprise-level red team engagement can exceed $100,000.
Monthly Retainer — Best for ongoing advisory relationships, vCISO services, and managed services. Retainers create predictable recurring revenue, which makes your business more stable and valuable. vCISO retainers typically range from $3,000 to $20,000 per month depending on engagement scope.
Subscription/MRR (MSSP Model) — Best for managed security services with ongoing monitoring, alerting, and response. Pricing is typically per device, per user, or per endpoint, and creates strong recurring revenue.
Pricing Strategy Tips
- Research competitors in your geographic market and niche
- Never compete solely on price — it is a race to the bottom that devalues the industry
- Charge based on the value you deliver (risk reduction, compliance achievement, breach prevention), not just your time
- Offer tiered service packages to accommodate clients with different budgets
- Build scope creep protections into all contracts
Step 9: Set Up Operations and Tech Stack
Professional operations from day one build client confidence and protect your own business.
Essential Tools and Platforms
Security Testing and Monitoring:
- Kali Linux — The standard platform for penetration testing
- Metasploit — Penetration testing framework
- Burp Suite — Web application security testing
- Nessus / Qualys — Vulnerability scanners
- Splunk / Microsoft Sentinel / Elastic SIEM — Security information and event management
Business Operations:
- Project management: Asana, Monday.com, or Jira
- CRM: HubSpot (free tier is sufficient for early-stage), Salesforce for enterprise
- Time tracking and invoicing: FreshBooks, QuickBooks, or Harvest
- Secure communication: Signal, ProtonMail, or Microsoft Teams with proper security configurations
- Document management: SharePoint, Google Workspace with security controls enabled
- Password management: 1Password Teams or Bitwarden for Business
Legal and Compliance:
- Engagement letter templates reviewed by a technology attorney
- Non-disclosure agreements (NDAs)
- Scope of work (SOW) templates with clear deliverables and limitations of liability
- Data processing agreements for clients subject to GDPR
Pro tip: Practice what you preach. Your own security posture must be exemplary. Implement multi-factor authentication on all accounts, use encrypted communication, maintain secure backups, and develop and document your own security policies. Being breached as a cybersecurity company would be catastrophic for your reputation.
Step 10: Market Your Cybersecurity Business
Marketing a cybersecurity company requires a strategy built on trust, credibility, and education. Unlike consumer products, cybersecurity services are bought by risk-averse buyers who research thoroughly before committing.
Build Your Digital Presence
Professional Website — Your website is your primary sales tool. It must communicate your services, credentials, target clients, and results clearly. Include case studies (with client permission), team bios with certifications, and clear calls to action.
Search Engine Optimization (SEO) — Create educational blog content that answers the questions your target clients are searching for: “How to protect my business from ransomware,” “HIPAA cybersecurity requirements,” “What is a penetration test?” High-quality educational content drives organic traffic and positions you as an authority.
LinkedIn — LinkedIn is the most important social platform for B2B cybersecurity marketing. Publish thought leadership content regularly, engage in relevant groups, and build connections with target decision-makers (CISOs, CTOs, CEOs, IT Directors, and compliance officers).
Content Marketing — Create whitepapers, security guides, webinars, and videos that provide genuine value to your target audience. Ungated content builds trust faster than gated lead generation content.
Build Your Reputation
Speak at conferences — Local BSides events, ISACA chapter meetings, and industry conferences are excellent venues for establishing thought leadership and meeting prospects.
Publish research — If you discover vulnerabilities, responsibly disclose them and publish writeups. Original security research earns enormous credibility in the industry.
Get listed on relevant directories — MSSP Alert, Clutch, G2, and government contractor databases like SAM.gov can drive inbound inquiries.
Earn reviews and testimonials — Client testimonials are powerful social proof. Ask satisfied clients to provide references and written testimonials that you can feature on your website.
Develop referral partnerships — Partner with IT service providers, managed service providers (MSPs), law firms specializing in data privacy, and accounting firms whose clients need cybersecurity. These referral relationships can be a significant and low-cost source of new business.
Step 11: Land Your First Clients
The hardest part of starting any services business is landing the first few clients. Here is how to break through:
Start with your existing network — Your first clients will almost certainly come from people who already know and trust you: former colleagues, employers, friends, or family members who own businesses. Make sure everyone in your network knows what you are doing and who you help.
Offer a limited free or discounted engagement — Consider offering a free vulnerability scan, a complimentary security review, or a discounted initial assessment to one or two anchor clients who will give you a strong testimonial and possibly a referral.
Target small businesses in your local area — Local businesses are often underserved by large cybersecurity firms. A personal, local approach — even attending local business networking events — can be remarkably effective.
Pursue government contracts — Register on SAM.gov (the System for Award Management) to be eligible for federal, state, and local government contracts. Many government agencies are actively seeking cybersecurity support, and small business set-asides create genuine opportunities for new entrants.
Respond to RFPs (Requests for Proposals) — Monitor government and private sector RFP databases. While winning an RFP cold is difficult, the process teaches you what clients need and positions you for future opportunities.
Use LinkedIn strategically — Reach out directly to decision-makers at target companies. Do not pitch immediately — build a relationship first by engaging with their content and sharing relevant insights.
Step 12: Scale and Grow
Once you have established a client base and proven your service model, it is time to think about scaling.
Productize your services — Rather than delivering every engagement as a completely custom effort, develop standardized service packages with defined methodologies, deliverables, and timelines. This increases efficiency and makes it easier to train new team members.
Build recurring revenue — Every services business should move toward a retainer or subscription model where possible. Recurring revenue makes your company more predictable, more valuable, and more resilient.
Develop strategic partnerships — Technology vendor partnerships (with companies like CrowdStrike, Palo Alto Networks, SentinelOne, or Microsoft) can provide additional revenue through reseller margins, co-marketing opportunities, and deal referrals.
Invest in marketing and sales infrastructure — As you grow, systematic lead generation and sales processes replace relationship-based selling. Hire or contract dedicated business development resources.
Consider acquisitions — Acquiring a smaller competitor or a complementary business can accelerate growth, expand your service portfolio, or add key talent faster than organic hiring.
Monitor your financial health obsessively — Track your key metrics monthly: monthly recurring revenue (MRR), client acquisition cost, average contract value, churn rate, gross margin, and days sales outstanding (DSO). These numbers tell you where your business is healthy and where it needs attention.
For ongoing education on running a professional services business, consider resources like Harvard Business Review and the MIT Sloan Management Review, both of which regularly publish research on entrepreneurship, services business management, and technology strategy.
Common Mistakes to Avoid {#mistakes}
Trying to be everything to everyone — Lack of focus dilutes your expertise, your marketing, and your credibility. Pick a niche and own it.
Underpricing your services — Many new cybersecurity consultants undercharge because they are nervous about losing deals. Underpricing signals low value and attracts clients who will not value your work. Price confidently based on the outcomes you deliver.
Skipping contracts and clear scope of work — Scope creep will destroy your profitability. Always work with a clear, signed contract that defines deliverables, timelines, and what is explicitly out of scope.
Neglecting your own security — A cybersecurity firm that gets breached faces existential reputational damage. Treat your own security with the same rigor you apply to clients.
Growing headcount too fast — Hiring ahead of revenue is one of the most common ways startups run out of cash. Keep your team lean until revenue clearly supports expansion.
Ignoring compliance and insurance — One lawsuit or regulatory action can end a small business. Get appropriate professional liability insurance and understand the compliance obligations your business has to clients’ data.
Poor client communication — Cybersecurity is technical, and clients are often non-technical. Translating complex findings into clear, actionable business language is a skill that sets great firms apart from mediocre ones.
Frequently Asked Questions :
How much does it cost to start a cybersecurity company? A solo consulting practice can be launched for as little as $5,000–$15,000, covering certifications, software tools, website, legal setup, and initial marketing. An MSSP or product company will require $50,000–$500,000 or more depending on staffing, tooling, and infrastructure requirements.
Do I need a degree to start a cybersecurity company? A degree is not legally required, but it strengthens your credibility. In practice, relevant certifications (CISSP, CEH, Security+) and demonstrable experience are what clients and hiring managers care most about. Many successful founders built their reputation through certifications and hands-on work rather than formal degrees.
How long does it take to start a cybersecurity company? The legal and administrative setup (LLC registration, bank account, insurance) can be completed in 2–4 weeks. Building your first client base typically takes 3–12 months. Growing to a team of 5–10 people with a stable client roster typically takes 2–3 years.
Is the cybersecurity market too competitive? The market is competitive, but it is far from saturated. Demand is growing faster than supply across nearly every segment and geography. Specialization in a specific niche, industry, or service type allows even new entrants to carve out a defensible position.
What is the most profitable cybersecurity service to offer? Penetration testing and red team engagements can be highly profitable due to the specialized expertise required and the clear, valuable deliverables. vCISO services offer excellent recurring revenue potential. Managed security services (MSSP) generate strong monthly recurring revenue at scale but require significant upfront infrastructure investment.
Do I need a cybersecurity license to start? There is currently no federal license required specifically for cybersecurity services in the United States, though this may evolve as the regulatory landscape develops. You will need a general business license from your local jurisdiction and may need sector-specific authorizations depending on your client base (for example, handling classified government data requires security clearances).
Final Thoughts
Starting a cybersecurity company is one of the most strategically sound business decisions you can make in 2026. The market is enormous, the demand is structural and growing, the margins are strong, and the work is genuinely meaningful you are helping protect businesses, individuals, and institutions from real harm.
But success requires more than technical skill. You need business acumen, client communication skills, a focused niche strategy, financial discipline, and a relentless commitment to your own continuous learning. The cybersecurity industry rewards expertise and reputation above all else.
Follow the 12 steps outlined in this guide:
- Build your skills and earn industry-recognized certifications
- Choose a focused niche
- Write a thorough business plan
- Select the right legal structure
- Register and license your business
- Secure appropriate funding
- Build a talented, trustworthy team
- Define your services and price them confidently
- Set up professional operations and your tech stack
- Market consistently and authentically
- Land your first clients through your network and targeted outreach
- Scale deliberately with recurring revenue and strong financial management
The cybersecurity talent gap is real, the market opportunity is massive, and the need for skilled, ethical security professionals has never been greater. If you have the knowledge, the drive, and the discipline to execute, there is no better time to build the cybersecurity company you have been thinking about.
Recommended External Resources
- NIST National Initiative for Cybersecurity Education (NICE) — Frameworks, career pathways, and education resources from the U.S. government’s leading standards body
- ISC2 Certifications — Home of the CISSP, CCSP, and other premier cybersecurity certifications
- U.S. Small Business Administration — Business planning templates, loan programs, and small business resources
- SANS Institute — World-leading cybersecurity training and research organization
- CISA (Cybersecurity and Infrastructure Security Agency) — Official U.S. government cybersecurity guidance, resources, and best practices
- MIT Sloan Management Review — Cybersecurity Research-backed insights on cybersecurity strategy and business management
- Harvard Business Review — Entrepreneurship Essential reading for building and scaling a services business