Quick Answer
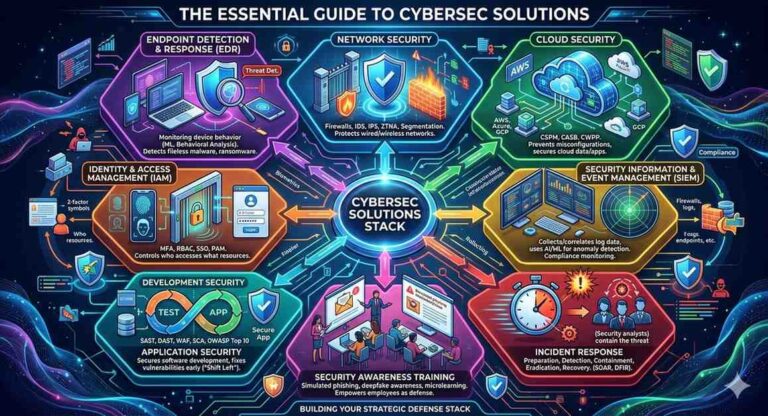
Cybersec solutions are the tools, technologies, frameworks, and strategies organizations use to detect, prevent, and respond to cyber threats. The most essential cybersec solutions in 2026 include network security platforms, endpoint detection and response (EDR) tools, cloud security systems, identity and access management (IAM), Security Information and Event Management (SIEM), and Zero Trust architecture. This guide explains each solution in detail so you can build the right defense stack for your organization.
What Are Cybersec Solutions?
Cybersec solutions refer to the full range of technologies and practices designed to protect digital systems, networks, data, and users from unauthorized access, theft, damage, or disruption.
The term covers everything from a basic firewall protecting a small business network, to a full Security Operations Center (SOC) running 24/7 threat monitoring for a global enterprise. As cyberattacks grow more sophisticated, the definition of “cybersec solutions” has expanded beyond simple software tools into a holistic, strategic discipline.
According to IBM’s 2026 Guide to Cybersecurity, cybersecurity today encompasses a wide range of functions, from basic password protections and security hygiene to sophisticated offensive tests and AI-powered threat detection tools. The ultimate goal is to protect computer systems, applications, devices, financial assets, and people against malicious actors and the ever-evolving tactics they deploy.
In 2026, the stakes have never been higher. Global cybercrime costs are projected to exceed $10.5 trillion annually. A data breach now costs businesses an average of $4.45 million. And with AI-powered attacks becoming mainstream, organizations that rely on outdated tools are dangerously exposed.
Why Cybersec Solutions Matter More Than Ever in 2026
The threat landscape of 2026 looks fundamentally different from even three years ago. Several forces are driving this change:
Artificial Intelligence on Both Sides: Attackers now use AI to generate highly convincing phishing emails, automate vulnerability scanning, create deepfake audio and video for fraud, and launch attacks at a speed no human team can match. Defenders are using AI to detect threats in real time and automate responses, but the arms race is intense.
Cloud Adoption Has Expanded the Attack Surface: As businesses moved operations to AWS, Azure, and Google Cloud, they created thousands of new potential entry points. Cloud misconfiguration alone is now the leading cause of data breaches worldwide.
Remote Work Eliminated the Traditional Perimeter: When every employee is a potential endpoint and every home network is a potential vulnerability, traditional firewall-based security is no longer enough. Organizations need solutions that protect users and data wherever they are.
Ransomware Became an Industry: Ransomware-as-a-Service (RaaS) platforms allow even non-technical criminals to launch sophisticated attacks. Hospitals, schools, and critical infrastructure are all targeted daily.
Regulatory Pressure Is Increasing: GDPR, HIPAA, PCI DSS, NIST, and dozens of new country-level regulations now require organizations to implement documented, verifiable cybersecurity programs. Non-compliance carries both financial penalties and criminal liability.
Understanding and implementing the right cybersec solutions is no longer optional. It is a fundamental requirement for staying operational in 2026.
The 8 Core Cybersec Solutions Every Organization Needs
1. Network Security Solutions
Network security is the foundation layer of any cybersec strategy. It protects the infrastructure across which all data travels, including wired networks, wireless networks, and the internet connections that link your organization to the outside world.
What it includes:
Firewalls filter incoming and outgoing traffic based on defined security rules, blocking suspicious connections before they reach your systems. Modern Next-Generation Firewalls (NGFWs) go beyond basic packet filtering to inspect application-layer traffic, detect intrusions, and integrate threat intelligence feeds.
Intrusion Detection Systems (IDS) monitor network traffic for signs of known attack patterns and alert security teams. Intrusion Prevention Systems (IPS) take this a step further by automatically blocking detected threats in real time.
Network segmentation divides your network into isolated zones so that if one area is compromised, attackers cannot freely move to other systems. This limits what security professionals call “lateral movement,” which is one of the most damaging behaviors in a breach scenario.
The Zero Trust standard for 2026: Traditional network security assumed that anything inside the network perimeter could be trusted. Zero Trust Network Access (ZTNA) rejects that assumption entirely. Under ZTNA, every user, every device, and every access request must be continuously verified, regardless of location. This model has become the standard for enterprise network security in 2026.
As the NIST Cybersecurity Framework emphasizes, network protection must be built around the principles of least privilege access and continuous monitoring, not just static rules.
2. Endpoint Detection and Response (EDR)
Every laptop, desktop, smartphone, tablet, and IoT device that connects to your network is an endpoint, and every endpoint is a potential entry point for attackers.
Traditional antivirus software compares files against a database of known malware signatures. This approach fails against modern threats because it cannot detect what it has never seen before. EDR platforms replaced antivirus as the endpoint security standard.
How EDR works:
EDR tools run continuously on each device, monitoring behavior rather than just scanning files. Using machine learning and behavioral analysis, EDR can detect when a process is behaving suspiciously, even if it has never been categorized as malware. It can isolate a compromised device from the network, kill malicious processes, and alert security teams, all automatically and within seconds.
Fileless malware, which runs entirely in memory without writing files to disk, is completely invisible to traditional antivirus tools. EDR detects it by flagging the unusual behavior of the process running in memory.
Leading EDR platforms in 2026 include CrowdStrike Falcon, SentinelOne, and Microsoft Defender for Endpoint. The SANS Institute reports that endpoint attacks account for more than 70 percent of successful data breaches, making EDR one of the most critical investments any organization can make.
3. Cloud Security Solutions
Cloud security protects the data, applications, and infrastructure hosted in cloud environments. With most enterprise operations now running on cloud platforms, cloud security has become one of the most critical and complex areas of cybersec.
Cloud Security Posture Management (CSPM): CSPM tools continuously scan your cloud environment for misconfigurations, exposed storage buckets, overpermissioned accounts, and compliance violations. They provide real-time visibility into your cloud security posture and automatically flag or remediate issues before attackers can exploit them.
Cloud Access Security Broker (CASB): A CASB sits between your users and cloud services, enforcing security policies, detecting shadow IT (unauthorized cloud tools used by employees), and monitoring data movement in and out of cloud applications.
Cloud Workload Protection Platform (CWPP): CWPP solutions protect the servers, containers, and serverless functions running inside your cloud environments, detecting threats at the workload level.
The Cloud Security Alliance consistently identifies misconfiguration as the top cloud security threat. A single improperly configured storage bucket or exposed API key can expose millions of records. CSPM tools are the primary defense against this risk.
4. Identity and Access Management (IAM)
Identity is the new perimeter. In 2026, the majority of successful attacks begin not with a technical exploit but with compromised credentials. Attackers steal a username and password, log in through a legitimate channel, and then quietly escalate their access and move through the system.
IAM solutions control who can access what resources, under what conditions, and for how long.
Core components of an IAM solution:
Multi-Factor Authentication (MFA) requires users to verify their identity through at least two factors: something they know (a password), something they have (a phone or hardware key), or something they are (a fingerprint or face scan). MFA alone blocks more than 99 percent of automated credential attacks.
Role-Based Access Control (RBAC) assigns permissions based on job role, ensuring that employees only have access to the systems and data they need to do their specific job, and nothing more. This is the principle of least privilege in action.
Privileged Access Management (PAM) provides additional controls around accounts with elevated system access, such as IT administrators and database managers. These accounts are prime targets for attackers because they carry so much power.
Single Sign-On (SSO) allows users to authenticate once and access all their authorized tools without logging in separately to each one. SSO reduces password fatigue and makes security policy enforcement far more manageable.
5. Security Information and Event Management (SIEM)
A SIEM platform collects log data from every source across your IT environment: firewalls, servers, applications, cloud services, endpoints, and more. It aggregates all of this data in one place, correlates events across sources, and uses analytics to detect patterns that indicate a threat.
Without SIEM, a security team might have hundreds of separate log files from different systems and no practical way to connect the dots between them. A SIEM turns that fragmented data into a unified security intelligence picture.
Modern SIEM in 2026: AI-powered SIEM platforms now go beyond rule-based detection to use machine learning for anomaly detection. They can identify when a user’s behavior deviates from their normal pattern, for example, downloading 10x their usual volume of files or accessing systems at unusual hours, and flag it for investigation.
SIEM also plays a critical role in regulatory compliance. Most frameworks, including NIST, HIPAA, and PCI DSS, require organizations to maintain detailed security logs and demonstrate that they are monitoring for threats. SIEM automates this requirement.
Leading SIEM solutions include Splunk, Microsoft Sentinel, IBM QRadar, and Elastic Security.
6. Application Security Solutions
Every application your organization uses or builds is a potential attack surface. Application security (AppSec) focuses on finding and fixing vulnerabilities in software before attackers can exploit them.
Static Application Security Testing (SAST) analyzes source code for vulnerabilities during the development process, before the application is ever run. It catches issues like SQL injection vulnerabilities, insecure data handling, and hardcoded credentials early, when they are cheapest to fix.
Dynamic Application Security Testing (DAST) tests running applications by simulating real attacks. It checks how the application behaves under attack conditions and identifies vulnerabilities that only appear when the app is live.
Web Application Firewalls (WAF) sit in front of web applications and filter malicious requests in real time. They protect against the OWASP Top 10 vulnerabilities, including SQL injection, Cross-Site Scripting (XSS), and broken authentication.
The Open Web Application Security Project (OWASP) publishes the OWASP Top 10, the globally recognized standard for the most critical web application security risks. Every development team and security professional should use the OWASP Top 10 as a foundational benchmark for application security.
Software Composition Analysis (SCA) tools have become essential in 2026 due to the rise of supply chain attacks. SCA scans the open-source libraries and third-party components your applications rely on, flagging any that contain known vulnerabilities.
7. Incident Response Solutions
Incident response (IR) solutions are the tools and processes that help organizations detect, contain, and recover from cyber attacks. Every organization will eventually experience a security incident. The question is not whether a breach will happen, but how quickly and effectively you can respond when it does.
A well-structured incident response program includes four phases: preparation, detection and analysis, containment and eradication, and recovery and post-incident review.
Security Orchestration, Automation, and Response (SOAR) platforms automate repetitive incident response tasks. When an EDR tool detects a compromised endpoint, a SOAR platform can automatically isolate that endpoint from the network, notify the security team, create a ticketing record, and begin a predefined response playbook, all within seconds and without requiring human intervention for each step.
Digital Forensics and Incident Response (DFIR) tools help security teams investigate the root cause of a breach, preserve evidence for legal proceedings, and understand exactly what happened so they can prevent it from recurring.
According to MIT Lincoln Laboratory’s cybersecurity research division, organizations with a tested incident response plan reduce their breach costs by an average of 35 percent compared to those with no plan in place. This makes incident response planning one of the highest-return investments in cybersec.
8. Security Awareness Training
Technology can block many threats, but human error remains the root cause of approximately 95 percent of all successful cyber attacks. Security awareness training transforms your employees from a vulnerability into a first line of defense.
Modern security awareness training goes far beyond an annual compliance video. Effective programs in 2026 use:
Simulated phishing campaigns that send realistic, fake phishing emails to employees and provide immediate, educational feedback when someone clicks. Organizations that run monthly simulations reduce click-through rates on real phishing emails by more than 70 percent.
Deepfake awareness training to help employees recognize AI-generated audio and video used in social engineering attacks. With deepfake technology now accessible to criminals, teaching employees to verify requests through out-of-band channels (calling back on a known number, not the one in the message) is essential.
Ongoing microlearning that delivers short, focused lessons regularly rather than one long annual session. This approach dramatically improves retention and keeps security top of mind.
The Cybersecurity and Infrastructure Security Agency (CISA) lists employee awareness and training as one of the most impactful cybersecurity investments an organization can make, regardless of size or industry.
How to Build a Cybersec Solutions Stack for Your Organization
Building the right cybersec solutions stack depends on the size of your organization, your industry, your budget, and the specific threats most relevant to your environment. Here is a practical framework:
Step 1: Conduct a Risk Assessment. Identify your most critical digital assets, the threats most likely to target them, and your current security gaps. Use the NIST Cybersecurity Framework as your benchmark.
Step 2: Start with the Fundamentals. Before deploying sophisticated tools, ensure the basics are in place. MFA on all accounts, patched software across all systems, regular data backups with tested restore procedures, and a documented incident response plan. These four controls alone eliminate the majority of common attacks.
Step 3: Prioritize Based on Your Environment. A remote-first company should prioritize EDR and IAM. A software company needs strong AppSec. A healthcare organization must prioritize network segmentation and HIPAA-compliant data protection. A company running heavily on cloud services needs CSPM and CASB as core priorities.
Step 4: Layer Your Defenses. No single tool provides complete protection. Deploy solutions that complement each other so that if one layer fails, the others continue to function. This strategy, known as Defense in Depth, is the gold standard in cybersecurity architecture.
Step 5: Measure and Improve Continuously. Run penetration tests regularly to validate that your controls actually work. Review your SIEM alerts for patterns. Track your mean time to detect (MTTD) and mean time to respond (MTTR) as key performance indicators. Cybersec is not a one-time project. It is an ongoing program.
Cybersec Solutions Comparison: Quick Reference Table
| Solution | Primary Function | Best For | Key Tools in 2026 |
|---|---|---|---|
| Network Security | Protecting data in transit | All organizations | Palo Alto, Cisco, ZTNA |
| EDR | Protecting devices and endpoints | Remote-first businesses | CrowdStrike, SentinelOne |
| Cloud Security | Securing cloud infrastructure | SaaS companies, enterprises | CSPM, CASB, CWPP tools |
| IAM | Controlling access and identity | All organizations | Okta, Azure AD, CyberArk |
| SIEM | Centralizing threat detection | Mid to large enterprises | Splunk, Microsoft Sentinel |
| Application Security | Securing software and APIs | Development teams | SAST, DAST, WAF, SCA |
| Incident Response | Managing and recovering from breaches | All organizations | SOAR, DFIR platforms |
| Security Awareness Training | Reducing human error | All organizations | KnowBe4, Proofpoint |
Frequently Asked Questions About Cybersec Solutions
What is the difference between cybersecurity and cybersec solutions?
Cybersecurity is the broader discipline and field of practice. Cybersec solutions are the specific tools, technologies, and frameworks used to implement cybersecurity in practice. Cybersecurity is the goal; cybersec solutions are the means to achieve it.
What cybersec solutions do small businesses need most?
Small businesses should start with MFA on all accounts, an EDR tool on all devices, automated patch management, regular data backups with tested restores, and basic security awareness training for all employees. These five controls address the most common attack vectors at a manageable cost.
How much do cybersec solutions cost?
Costs vary widely. A basic security stack for a small business can run $1,000 to $5,000 per year. A full enterprise-grade solution including SIEM, EDR, cloud security, and a managed SOC can cost $50,000 to several million dollars per year depending on scale. The cost of a breach, averaging $4.45 million, consistently exceeds the cost of prevention for organizations of any size.
What is Zero Trust and why is it important?
Zero Trust is a security model built on the principle of “never trust, always verify.” Rather than assuming that anything inside your network is safe, Zero Trust requires continuous verification of every user, every device, and every access request. It is the most important architectural shift in cybersecurity since the invention of the firewall and is now considered the baseline standard for enterprise security in 2026.
What is a Security Operations Center (SOC)?
A SOC is a team of cybersecurity professionals who monitor, detect, analyze, and respond to security threats on a continuous, 24/7 basis. SOC teams use SIEM, SOAR, and threat intelligence platforms to maintain visibility across an organization’s entire environment. Organizations that cannot build an internal SOC often use Managed Security Service Providers (MSSPs) to outsource this function.
Are AI-powered cybersec solutions worth it in 2026?
Yes, for most organizations operating at medium to enterprise scale. AI-powered tools dramatically reduce the time required to detect and respond to threats. The average time to identify and contain a breach without AI-assisted tools is 277 days. Organizations using AI-powered detection reduce that number significantly. The key is choosing tools where AI is genuinely embedded in the detection logic, not just marketed as a feature.
Final Thoughts
Cybersec solutions are not a single product you buy and install once. They are a layered, continuously evolving defense program built from complementary tools and informed by a clear understanding of your organization’s specific risks.
The eight core solutions covered in this guide, including network security, EDR, cloud security, IAM, SIEM, application security, incident response, and security awareness training, form the foundation of a complete cybersec strategy. Most organizations need some combination of all of them, prioritized based on their environment, their risk profile, and their budget.
Start with a risk assessment. Layer your defenses. Train your people. Test your controls regularly. And use the frameworks published by trusted authorities like NIST, CISA, and OWASP to benchmark and continuously improve your security posture.
In 2026, cybersecurity is a business-critical function, not an IT afterthought. The organizations that treat it that way will be the ones that survive and thrive when attacks inevitably come.